Our TSA is supported in Microsoft Office, InfoPath and SharePoint. If you sign a document without a
digital timestamp, in this case when your personal certificate expires, Office reports on each document that you signed as
'Expired certificate - The certificate used to sign has expired'. If you timestamp your signatures, Office can reliably
determine when the signature was created prior to the certificate expiration. Timestamping your signatues is crucial if
your personal signing credentials were compromised - people could seperate which of your signatures are valid: those
signatures created before you "revoked" your signing certificate.
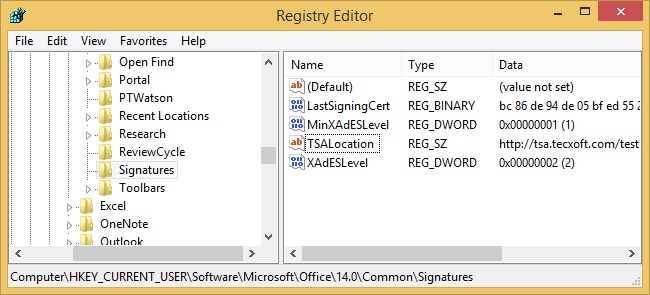
Minimum settings to enable timestamps in Office require to configure two entries in registry as described below.
You can open the Windows registry editor by executing the command regedit.
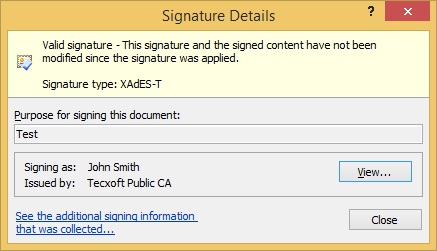
Signature Type should say as shown above "XAdES-T" to confirm the signature is timestamped. These values also confirm that there is a timestamp: XAdES-C XAdES-X XAdES-X-L